Every time you press play on your wireless headphones, something remarkable happens beneath the surface. Your phone and headphones engage in a choreographed dance across the radio spectrum, switching frequencies up to 1,600 times every second. This is frequency hopping spread spectrum (FHSS), and it’s the reason your Bluetooth connection survives in a world crowded with Wi-Fi networks, microwave ovens, and billions of other wireless devices.
The story of this technology traces back to a surprising origin: a Hollywood actress and an avant-garde composer. In 1942, Hedy Lamarr and George Antheil patented a “secret communication system” using frequency hopping to prevent radio-guided torpedoes from being jammed. The U.S. Navy initially dismissed their invention, but decades later, the same principle became fundamental to Bluetooth, Wi-Fi, and modern military communications. Lamarr’s contribution wasn’t the invention of frequency hopping itself—that had existed in various forms since the early 20th century—but her specific implementation using piano-roll mechanisms to synchronize hopping between transmitter and receiver.
The 79-Channel Strategy
Bluetooth operates in the 2.4 GHz ISM (Industrial, Scientific, Medical) band, spanning 2.400 to 2.4835 GHz. Rather than transmitting on a single frequency, Bluetooth divides this spectrum into 79 channels, each 1 MHz wide. When two devices connect, they don’t pick a channel and stay there. Instead, they hop between channels following a pseudo-random sequence determined by the master device’s clock and Bluetooth address.
This hopping happens at a furious pace. Bluetooth Classic hops 1,600 times per second, meaning each hop dwell is just 625 microseconds. During this brief window, a device transmits a packet and potentially receives a response before jumping to the next frequency. The hopping sequence appears random to outside observers but is entirely predictable to the paired devices—they both know exactly which channel to use at any given moment based on shared parameters.

Image source: Wikipedia - 2.4 GHz radio use
The diagram above shows how Wi-Fi occupies large contiguous swaths of spectrum (each Wi-Fi channel is 22 MHz wide). Bluetooth takes a fundamentally different approach: instead of claiming territory, it dances lightly across the entire band, never staying in one place long enough to be blocked.
Why Hopping Matters: Surviving the Interference War
The 2.4 GHz band is arguably the most congested slice of radio spectrum in existence. Wi-Fi networks dominate channels 1, 6, and 11 (each 22 MHz wide). Microwave ovens blast broadband interference around 2.45 GHz. Baby monitors, garage door openers, and countless IoT devices crowd into the same frequencies.
If Bluetooth used a fixed channel, it would face a simple problem: eventually, that channel would become unusable. A single Wi-Fi network on channel 6 would obliterate any Bluetooth transmission within its 22 MHz footprint. But with frequency hopping, Bluetooth spreads its risk across all 79 channels. Even if 20 channels are heavily interfered, the remaining 59 still work.
The mathematics are compelling. If interference corrupts 10% of channels, a single-frequency system would fail 10% of the time. With frequency hopping, packets are distributed across all channels, so only 10% of packets fail—and those can be retransmitted on clean channels.
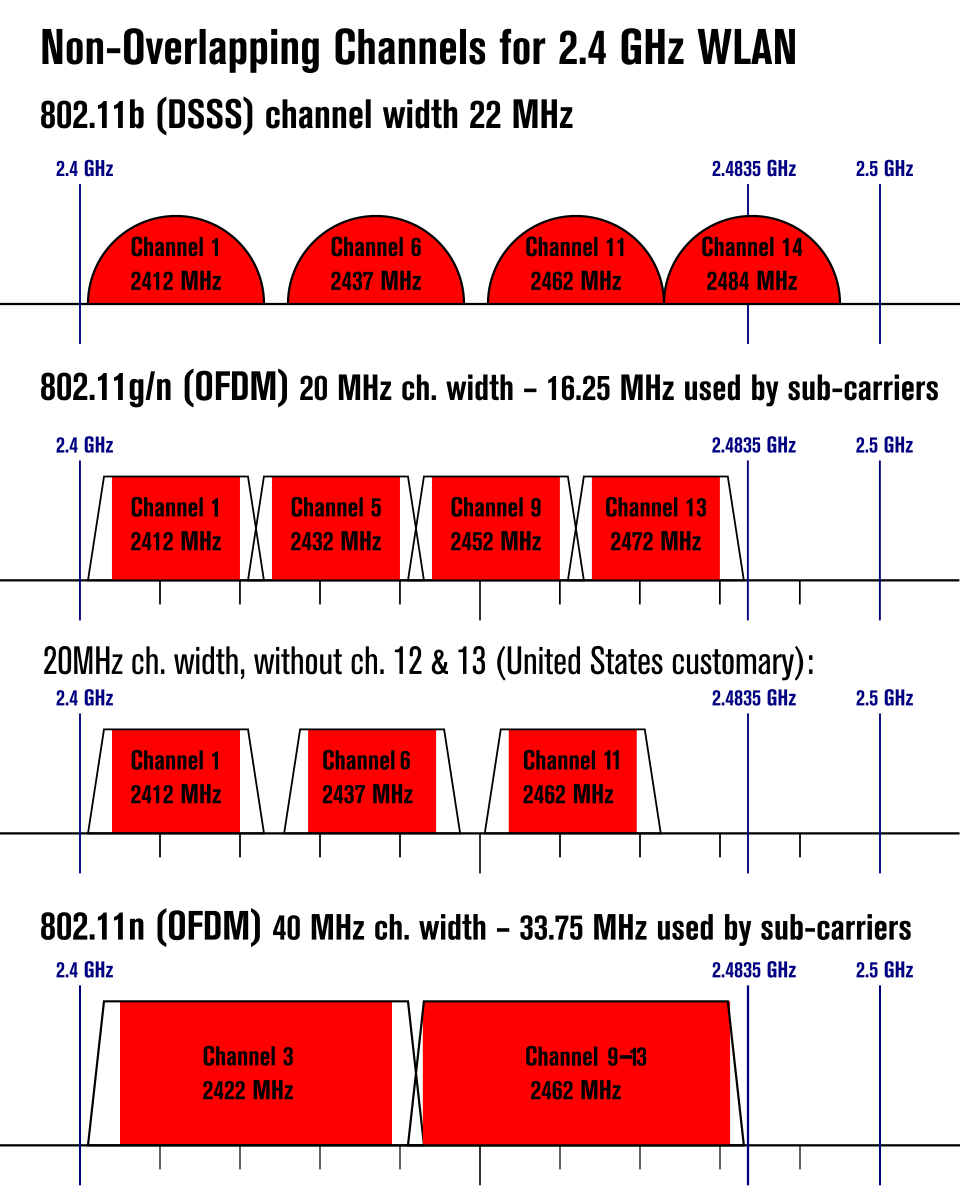
Image source: Wikipedia - List of WLAN channels
The figure above illustrates the non-overlapping channel allocations in the 2.4 GHz band. Notice how channels 1, 6, and 11 provide three clean Wi-Fi paths—but Bluetooth uses the spaces between and around them.
Adaptive Frequency Hopping: Learning from Failure
Standard frequency hopping is blind. It hops regardless of channel conditions, sometimes landing on frequencies clogged with interference. Bluetooth 1.2 introduced Adaptive Frequency Hopping (AFH), which makes the hopping intelligent.
AFH works by monitoring packet success rates on each channel. When a channel shows high packet loss or poor signal quality, devices mark it as “bad” and remove it from the hopping sequence. The channel map is continuously updated—channels can be blacklisted when degraded and reinstated when conditions improve.

Image source: Bluetooth SIG - Understanding Reliability
The diagram above shows AFH in action. The bottom axis shows channel indices and frequencies. Notice how communication spreads across available channels while avoiding congested ones. This adaptiveness is crucial for coexistence with Wi-Fi. A Bluetooth device can detect Wi-Fi activity on specific channels and simply route around them.
For Bluetooth Low Energy (BLE), the approach differs slightly. BLE uses 40 channels of 2 MHz width each. Three of these (channels 37, 38, and 39) are dedicated advertising channels for device discovery. The remaining 37 are data channels, and AFH can blacklist up to all but 2 of them if necessary.
gantt
title Bluetooth LE Channel Allocation in 2.4 GHz Band
dateFormat X
axisFormat %s
section Advertising Channels
Ch 37 (2402 MHz) :0, 2
Ch 38 (2426 MHz) :24, 2
Ch 39 (2480 MHz) :78, 2
section Data Channels
Ch 0-36 (2404-2478 MHz) :2, 76
The diagram above shows BLE’s channel structure. Notice how advertising channels (37, 38, 39) are strategically placed at the edges and middle of the spectrum—away from the most common Wi-Fi channels (1, 6, 11).
The Pairing Problem: Establishing Trust
Frequency hopping only works if both devices agree on the hopping sequence. This requires them to share cryptographic keys, which brings us to pairing—the process by which two devices establish a trusted relationship.
Early Bluetooth (versions 1.0 and 1.1) used a PIN-based pairing method that was fundamentally broken. Both devices would derive a link key from a user-entered PIN, but the derivation process transmitted enough information over the air that an attacker could brute-force the PIN in seconds. A 4-digit PIN offered only 10,000 possibilities.
Bluetooth 2.1 introduced Secure Simple Pairing (SSP), which fundamentally redesigned the security model. SSP uses elliptic curve cryptography to perform a Diffie-Hellman key exchange. Each device generates a public/private key pair. The public keys are exchanged over the air, and each device uses its private key and the other’s public key to compute a shared secret. Critically, this secret is never transmitted—both devices independently compute the same value.
SSP offers four association methods depending on device capabilities:
Numeric Comparison: Both devices display a 6-digit number, and users confirm they match. This provides man-in-the-middle protection because an attacker would need to simultaneously spoof different numbers on both devices.
Just Works: For devices without displays, this method provides encryption without man-in-the-middle protection. It’s used for simple accessories like headsets.
Passkey Entry: One device displays a passkey, and the user enters it on the other device. This provides authentication for devices with limited input capabilities.
Out of Band: Uses a separate channel (like NFC) to exchange pairing data, providing the strongest security.
The Protocol Stack: Layers Upon Layers
Bluetooth isn’t just a radio protocol—it’s a complete networking stack. Understanding it requires peeling back multiple layers.
At the bottom sits the Physical Layer (PHY). For Bluetooth Classic, this uses Gaussian Frequency Shift Keying (GFSK) modulation, achieving 1 Mbps raw data rate. Enhanced Data Rate (EDR) modes added in Bluetooth 2.0 use additional modulation schemes (π/4-DQPSK and 8DPSK) to reach 2 and 3 Mbps respectively.

Image source: Novel Bits - Bluetooth LE Protocol Stack
The Link Layer manages the radio state machine. In BLE, this includes states for standby, advertising, scanning, initiating, and connection. The link layer handles the timing-critical aspects of communication—when to transmit, when to listen, which channel to use.
The Logical Link Control and Adaptation Protocol (L2CAP) sits above the link layer, handling protocol multiplexing and packet segmentation. Higher-layer protocols like the Attribute Protocol (ATT) and Generic Attribute Profile (GATT) in BLE use L2CAP as their transport.
GATT defines how data is organized and accessed. Data is structured as services containing characteristics. A heart rate monitor might expose a Heart Rate Service with characteristics for measurement value, body sensor location, and control point. This standardized structure allows any device to discover and use services without prior knowledge.
Bluetooth Classic vs. Low Energy: Two Philosophies
Bluetooth Classic and Bluetooth Low Energy share a name and a frequency band, but they’re fundamentally different technologies designed for different purposes.
Bluetooth Classic is optimized for sustained, high-throughput connections. With EDR, it can achieve real-world throughput around 2-3 Mbps. It uses 79 channels and maintains continuous connections with active voice channels. This makes it ideal for audio streaming, file transfer, and applications requiring consistent bandwidth.
BLE takes the opposite approach. It’s designed for bursty, infrequent communication. A temperature sensor might wake up every few minutes, send a few bytes of data, and return to sleep. BLE achieves this through aggressive duty cycling—devices spend most of their time in low-power states, waking only briefly to communicate.
BLE uses only 40 channels (2 MHz each) compared to Classic’s 79 (1 MHz each). Its modulation is simpler, using GFSK only. Maximum raw data rate is 1 Mbps (2 Mbps in Bluetooth 5.0’s high-speed mode), but practical throughput is typically under 100-250 kbps. What BLE sacrifices in speed, it gains in power efficiency—a coin cell battery can power a BLE sensor for years.
Audio Latency: The Inevitable Delay
Bluetooth audio has a reputation for latency—the delay between when sound is produced and when you hear it. This latency isn’t a bug but a consequence of the design.
Several factors contribute to audio delay:
Codec Processing: Audio must be compressed before transmission. Advanced codecs like LDAC or aptX HD introduce more processing delay but offer better quality. SBC, the mandatory codec, has lower processing overhead but worse compression efficiency.
Transmission Time: Bluetooth’s packet structure and frequency hopping introduce inherent transmission delays. Each hop dwell of 625 microseconds adds to the total.
Buffering: Receivers maintain buffers to handle packet loss and retransmission. Larger buffers mean more robust playback but higher latency. Small buffers reduce latency at the cost of glitch susceptibility.
Signal Processing: Modern headphones include noise cancellation, equalization, and other DSP that adds milliseconds of delay.
Typical Bluetooth audio latency ranges from 40-200+ ms depending on codec and device implementation. This is imperceptible for music playback but noticeable for video (lip-sync issues) and problematic for gaming. Some codecs like aptX-LL (Low Latency) and LC3 (introduced with Bluetooth LE Audio) specifically target reduced latency, achieving under 40ms.
Version Evolution: Faster, Farther, More Efficient
Bluetooth has evolved dramatically since its 1999 debut. Each version has brought specific improvements:
Bluetooth 1.0/1.1 (1999): The original. Maximum 721 kbps, plagued by interoperability issues.
Bluetooth 1.2 (2003): Added Adaptive Frequency Hopping and improved voice quality.
Bluetooth 2.0/2.1 (2004/2007): Enhanced Data Rate brought 3 Mbps theoretical throughput. Bluetooth 2.1 introduced Secure Simple Pairing.
Bluetooth 3.0 + HS (2009): Added High Speed mode using an 802.11 link for large transfers (up to 24 Mbps), though Bluetooth itself remained the control channel.
Bluetooth 4.0 (2010): Introduced Bluetooth Low Energy, creating the dual-mode architecture we have today.
Bluetooth 5.0 (2016): Doubled BLE speed to 2 Mbps, quadrupled range (to ~240m theoretical), and added direction finding capabilities. Extended advertising enabled much larger broadcast messages.
Bluetooth 5.1 (2019): Added Angle of Arrival (AoA) and Angle of Departure (AoD) for centimeter-level positioning accuracy using antenna arrays.
Bluetooth 5.2 (2020): Introduced LE Audio with the LC3 codec, isochronous channels for synchronized audio streaming, and enhanced attribute protocol.
Bluetooth 5.3/5.4 (2021/2023): Refinements in connection subrating, encryption key size control, and advertising enhancements. Bluetooth 5.4 added encrypted advertising data.
Mesh Networking: Beyond Point-to-Point
Bluetooth’s original topology was the piconet: one master device coordinating up to seven active slaves. Multiple piconets could interconnect to form a scatternet, though this was rarely implemented in practice.
Bluetooth Mesh, introduced in 2017, fundamentally changed the topology. Instead of point-to-point connections, mesh enables many-to-many communication. Each node can relay messages to other nodes, extending range far beyond individual radio capabilities.
Image source: Bluetooth SIG - Mesh Networking
Mesh uses managed flooding for message delivery. When a node broadcasts a message, all nodes in range receive it. Relay nodes rebroadcast the message, and eventually it reaches the destination. A Time-To-Live (TTL) field prevents infinite loops. A message cache prevents duplicate processing.
This approach has trade-offs. Flooding is simple and robust—if multiple paths exist, the message will find its way—but not bandwidth-efficient. Every message occupies spectrum at every hop. Mesh is best suited for low-bandwidth, infrequent communication like building automation and industrial IoT.
Security in mesh is mandatory and multi-layered. All nodes share a Network Key (NetKey) for network-level encryption. Different Application Keys (AppKeys) secure specific applications. This separation means a light switch can relay messages for a security system without being able to decrypt their contents.
The Hidden Complexity of “Just Working”
When you pair headphones to your phone, you’re witnessing the result of decades of engineering evolution. Within seconds, the devices perform cryptographic handshakes, negotiate codecs, establish hopping sequences, and begin synchronized frequency hopping at 1,600 hops per second. AFH continuously monitors and avoids congested channels. Power management circuits wake and sleep radios in precise synchronization. All of this happens automatically, reliably, invisibly.
The technology’s success is measured by its invisibility. When Bluetooth works, you don’t think about it. When it doesn’t, you notice immediately. That’s the paradox of good wireless design: the better it works, the less anyone knows it’s there.
References
-
Bluetooth SIG. “How Bluetooth Technology Uses Adaptive Frequency Hopping to Overcome Packet Interference.” Bluetooth Technology Website, 2020.
-
Woolley, Martin. “Understanding Reliability in Bluetooth Technology.” Bluetooth SIG, 2020.
-
Ellisys. “Secure Simple Pairing Explained.” Ellisys Expert Notes EEN_BT07, 2011.
-
Bluetooth SIG. “Bluetooth Mesh Networking: An Introduction for Developers.” Version 1.0.1, December 2020.
-
National WWII Museum. “Hedy Lamarr’s WWII Invention Helped Shape Modern Tech.” April 2025.
-
IEEE. “Wi-Fi (IEEE 802.11) and Bluetooth Coexistence: Issues and Solutions.” IEEE Xplore.
-
Novel Bits. “The Bluetooth Low Energy Protocol Stack: Understanding the Layers.” July 2022.
-
SoundGuys. “Understanding Bluetooth Codecs.” May 2025.
-
Memfault. “A Practical Guide to BLE Throughput.” September 2019.
-
Bluetooth SIG. “Bluetooth Core Specification Version 5.4.” 2023.
-
Wikipedia. “2.4 GHz radio use.” Wikimedia Foundation, 2024.